How Google Meet keeps video conferences protected
Encrypted data and unique keys for meetings along with a two-step verification process, Google Meet has safeguards in place to keep hackers away
Everyone at home is counting heavily on video conferences for work and studies and even to keep in touch with friends who we cannot meet. No matter what we use video calls for, it is important that they are secure and not easily susceptible to attacks.
Of the many video conferencing apps we have been using lately, Google Meet is one of them. Google Meet has its security controls turned on by default (phew!) so as users don't have to do anything to ensure that the right protections are in place.
Protections to combat abuse and block hijacking attempts
Google Meet has an array of counter-abuse protections to keep meetings safe, including anti-hijacking measures for both web meetings and dial-ins.
Google Meet makes it difficult to programatically brute force meeting IDs (this is when a malicious individual attempts to guess the ID of a meeting and make an unauthorised attempt to join it) by using codes that are 10 characters long, with 25 characters in the set.
The app limits the ability of external participants to join a meeting more than 15 minutes in advance, reducing the window in which a brute force attack can even be attempted.
Also Read: Google Meet adding 2 million new users daily over past few weeks
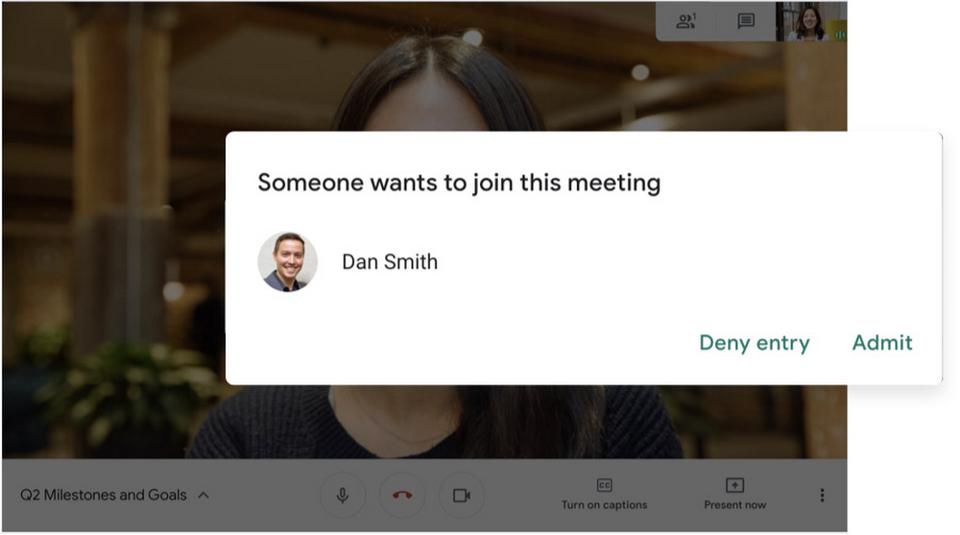
External participants cannot join meetings unless they're on the calendar invite or have been invited by in-domain participants. Otherwise, all participants must request to join the meeting, and their request must be accepted by a member of the host organisation.
Google is also rolling out some additional features for safety, some particularly for students and teachers, like -
- Only meeting creators and calendar owners can mute or remove other participants. This ensures that instructors can't be removed or muted by student participants.
- Only meeting creators and calendar owners can approve requests to join made by external participants. This means that students can't allow external participants to join via video, and that external participants can't join before the instructor.
- Meeting participants can't rejoin nicknamed meetings once the final participant has left. This means if the instructor is the last person to leave a nicknamed meeting, students can't join later without the instructor present.
Secure deployment and access controls for admins and end-users
To limit the attack surface and eliminate the need to push out frequent security patches, Google Meet works entirely in your browser. This means that the app does not require or ask for any plugins or software to be installed on Chrome, Firefox, Safari, or Microsoft Edge. For phones, the Google Meet app is recommended.
To help ensure that only authorized users administer and access Meet services, Google has multiple Two-Step Verification options for accounts that are secure and convenient. These include hardware and phone-based security keys and a Google prompt.
Additionally, Google Meet users can enroll their account on Advanced Protection Program (APP), which provides Google's strongest protections available against phishing and account hijacking and is specifically designed for the highest-risk accounts.
For G Suite Enterprise and G Suite for Education customers, Google offers Access Transparency, which logs any Google access to Google Meet recordings stored in Drive, along with the reason for the access (support team actions that you might have requested, for example).
Also Read: Google to integrate Meet with Gmail, likely to add Zoom-like gallery soon
Customers can also use data regions functionality to store select/covered data of Google Meet recordings in specific regions (i.e. US or Europe).
On Google Meet, all data is encrypted in transit by default between the client and Google for video meetings on a web browser, on the Android and iOS apps, and in meeting rooms with Google meeting room hardware. Google Meet also adheres to IETF security standards for Datagram Transport Layer Security (DTLS) and Secure Real-time Transport Protocol (SRTP).
For every person and for every meeting, Google Meet generates a unique encryption key, which only lives as long as the meeting, is never stored to disk, and is transmitted in an encrypted and secured RPC (remote procedure call) during the meeting setup.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.