Emotet, the world's most dangerous malware has been taken down
Emotet first appeared in 2014 as a banking Trojan, and it soon evolved to become one of the most powerful malware ever created.
The world's most dangerous malware botnet ‘Emotet' has been disrupted through a collective operation that spanned over two years. Emotet first appeared in 2014 as a banking Trojan, and it had since evolved into one of the most powerful malware ever created.
The global participation to take down Emotet involved Europol, UK's National Crime Agency, FBI, and law enforcement from Netherlands, France, Canada, Germany, Lithuania, and Ukraine. Soon after its discovery in 2014, Emotet had become “the go-to solution for cybercriminals over the years,” Europol said in a release.
Hackers could gain access to computer systems through Emotet and deploy activities such as data theft and extortion. The malware was transferred to users through infected email attachments. Hackers used different kinds of ways to make users open these malicious attachments, Europol added. Emotet email campaigns were also present in invoices, shipping notices and information about Covid-19.
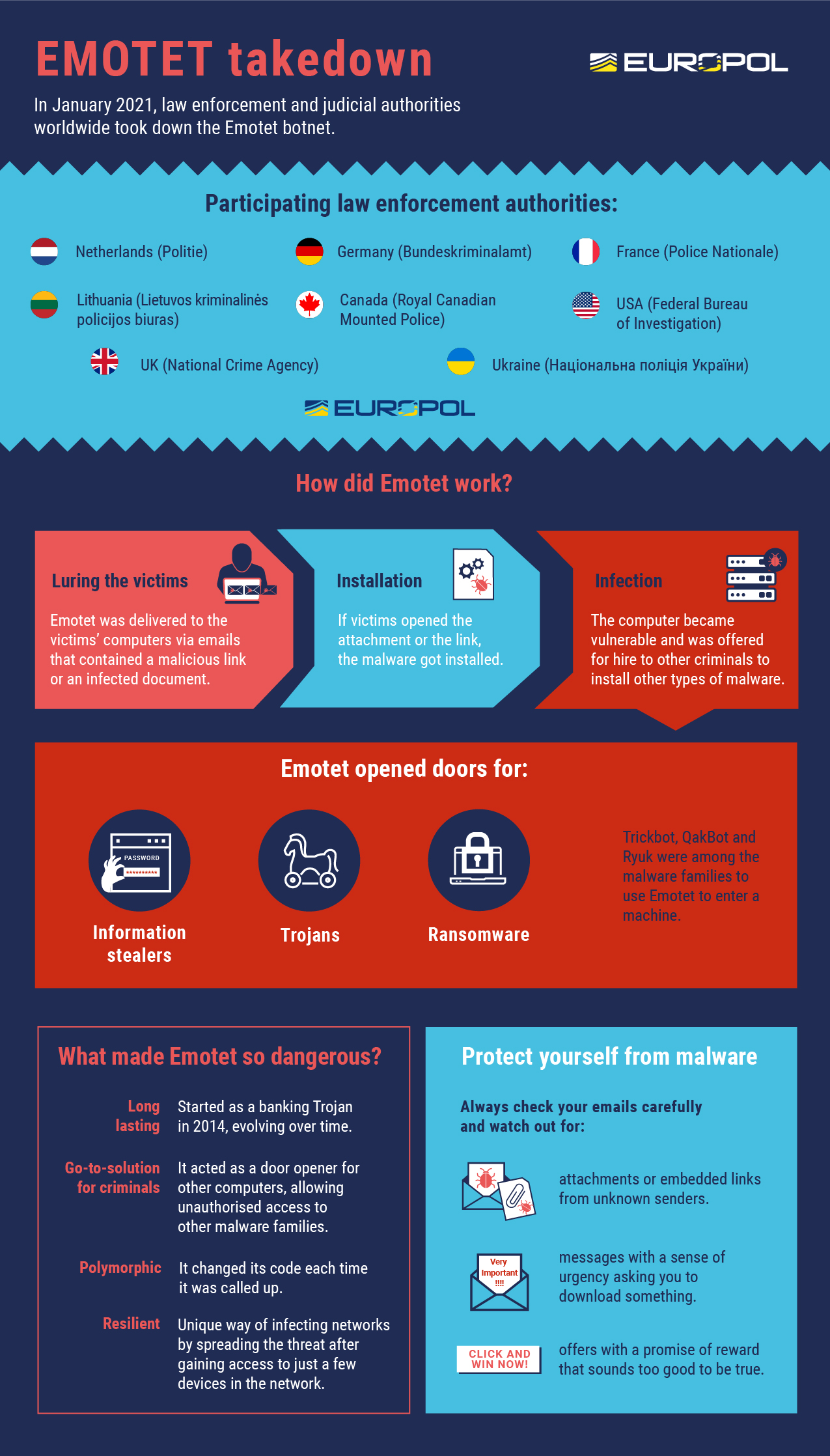
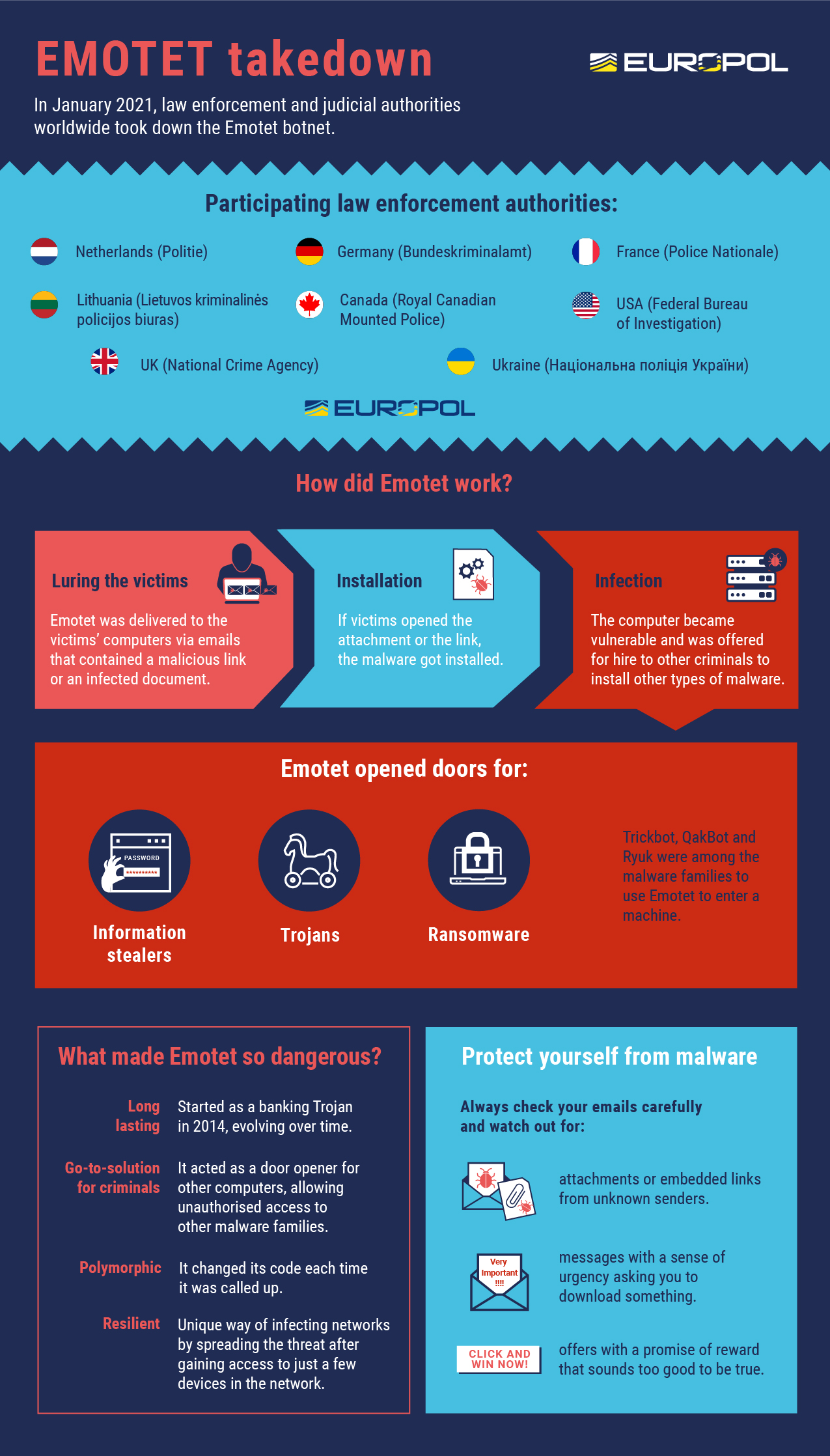
“All these emails contained malicious Word documents, either attached to the email itself or downloadable by clicking on a link within the email itself. Once a user opened one of these documents, they could be prompted to “enable macros” so that the malicious code hidden in the Word file could run and install EMOTET malware on a victim's computer,” Europol explained.
The reason why Emotet posed a bigger threat than other malware was due to the fact that it was offered to hire other cybercriminals to infect other systems with banking Trojans or ransomware. Other malware operators such as TrickBot and Ryuk are said to have benefited from Emotet.
The collective group of law enforcement took control of the infrastructure from the inside, and redirected the infected systems towards this infrastructure. Europol calls this “a unique and new approach to effectively disrupt the activities of the facilitators of cybercrime.”
Those who may have been affected by this malware can check this database containing email addresses, usernames and passwords stolen by Emotet. The information has also been distributed globally via CERTs.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.