Google removes malware that can read your WhatsApp messages and spreads using the ‘reply’ feature
The app promised the ability to play Netflix content from around the world. It then tricked users into granting permissions that it requires to work, and starts to spread itself with an ingenious method.
Malware appearing on the Google Play Store is not a new phenomenon and there are regular reports of infected applications acting in malicious ways every once in a while. A new application has appeared on the Google Play Store, which reportedly spreads itself via WhatsApp messages.
According to a recent analysis by Check Point Research, the malware that is spreading through the Play Store is a fake application that masquerades as a Netflix clone. Called FlixOnline, the app promises the ability to play Netflix content from around the world. It then tricks users into granting permissions that it requires to work, and starts to spread itself with an ingenious method.
Also read: A malware masquerading as System Update is attacking Android phones
The app connects to its command and control (C&C) server and then copies itself onto other devices by using the reply feature on WhatsApp messages. The company says that the app could have used the same method to spread further malware via malicious links, or steal data from user's WhatsApp accounts. It could also be used to perform phishing attacks, spread false news and malicious messages. It could also be used to extort users into paying money to prevent the malware from sending their chats to other accounts.
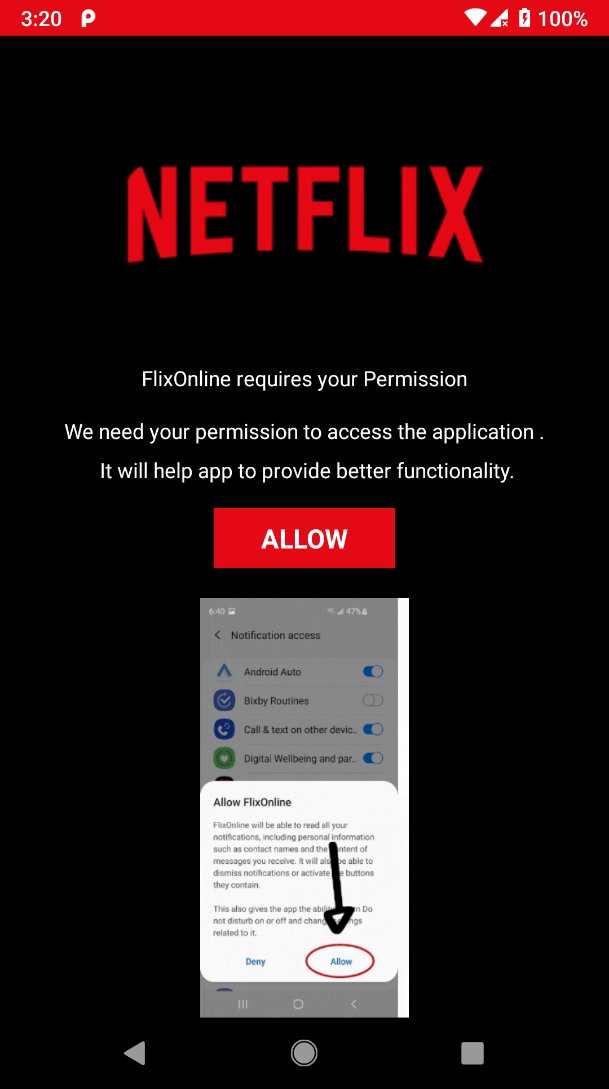
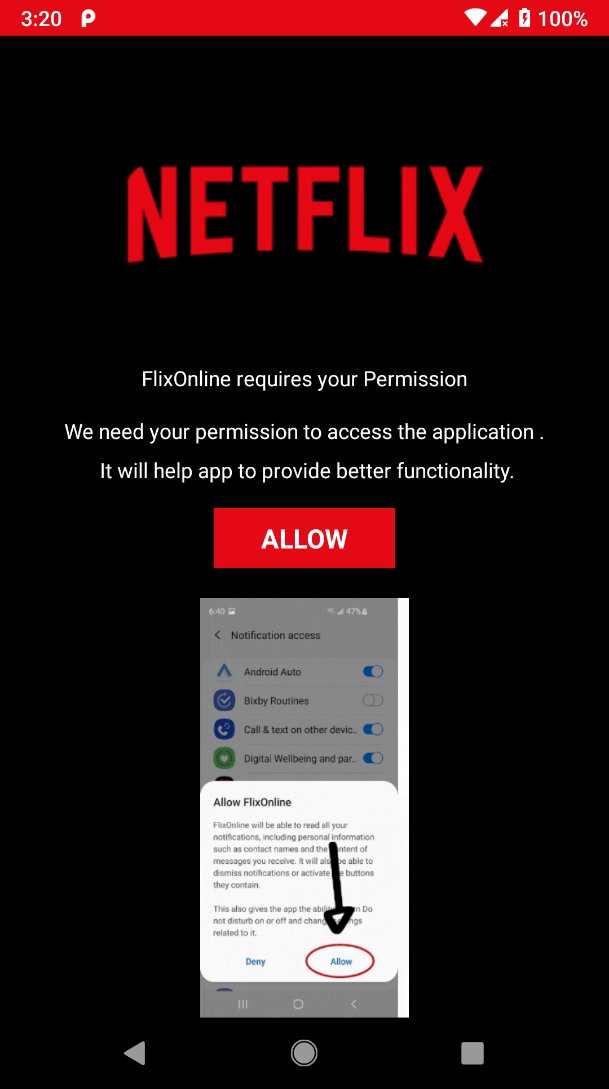
The app asks for three main permissions on order to work - ‘Overlay', ‘Battery Optimization Ignore', and ‘Notification' permissions. The overlay permission lets it draw over your existing app and fool the user into entering their credentials in the malicious app. Ignore battery optimisations is a self-protection method to protect it from Android's battery savings. The final ‘Notification' access permission will grant it the ultimate access to every notification and allowing the app to dismiss or reply to a message.
Read more: This dangerous Android malware can steal your banking info, warns CERT-In
Here's an example of the message that was forwarded to other users, also promising them two months of Netflix premium free: “2 Months of Netflix Premium Free at no cost For REASON OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix Premium Free anywhere in the world for 60 days. Get it now HERE https://bit[.]ly/3bDmzUw.” Users are advised to disregard any such messages they may receive.
Check Point says that after they disclosed the issue to Google, the company promptly removed it from the Play Store. The company estimates that the FlixOnline app was downloaded five hundred times over a two month period. Users should be aware of malware that can be spread through download links or attachments - even if they come from a trusted contact or a group.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.























