Meet Jann Horn, the 22-year-old who discovered the ‘biggest’ CPU security flaw in history
Here’s how a young security researcher discovered the biggest CPU security flaw impacting millions of devices worldwide.
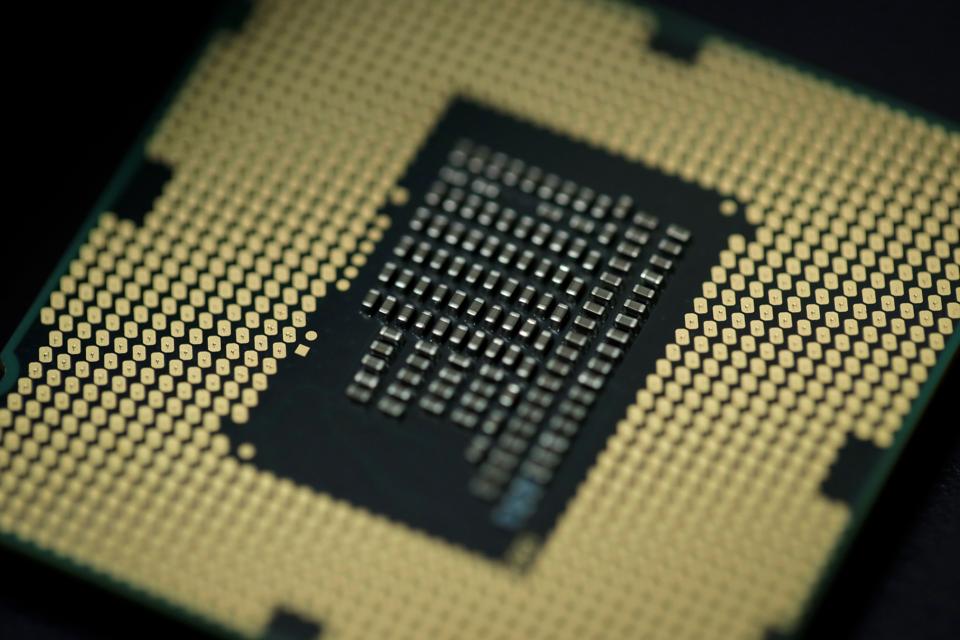
A major security loophole discovered by a 22-year-old has brought one of the biggest chipset companies in the world face-to-face with its worst PR crisis in a decade.
Zurich-based Jann Horn is a young security researcher associated with Google's Project Zero team, which discovered the Meltdown and Spectre CPU security flaws that impact millions of devices worldwide.
All major tech firms - including Intel, Microsoft and Apple - rushed to address the issue.
The discovery has changed things drastically for Horn. Now a celebrity, he received a rousing reception at an industry conference in Zurich last week, reported Bloomberg.
Horn had started studying lengthy manuals on chipsets last year. He narrowed down to one aspect, where he focused on how processors handle speculative execution. This technology essentially allows processors to guess which code will be necessary to execute the next step and starts processing ahead of the time. This includes fetching the necessary data.
"At this point, I realised that the code pattern we were working on might potentially leak secret data," Bloomberg quotes Horn as saying. "I then realised that this could - at least in theory - affect more than just the code snippet we were working on."
He then followed it up with investigations to find the two major security flaws in the chipsets.
Horn had a knack for spotting security flaws since his school days. His high school computer science teacher Wolfgang Reinfeld told Bloomberg that he had even spotted security flaws in his school's network. "Jann was, in my experience, always an outstanding mind," he said.
Prior to joining Google's elite security team, Horn worked with Berlin-based cybersecurity consultancy Cure53 - where he continued to work on security audits. Horn, however, is not the only young researcher to spearhead the security flaw's discovery.
Daniel Gruss, a 31-year-old security researcher Austria's Graz Technical University, independently found the security flaw. Gruss and his colleagues, Moritz Lipp and Michael Schwarz, worked together last year to come to a similar conclusion about the security of the chipsets.
"When I saw my private website addresses from Firefox being dumped by the tool I wrote, I was really shocked," he told Reuters. Last June, they published a paper titled KAISER, or Kernel Address Isolation to have Side-channels Effectively Removed. Later, their tool turned out to be an efficient defence mechanism against the Meltdown security flaw.
Despite stating that he did not know Horn was working on something similar, Gruss conceded that he found developing all this independently "incredibly impressive". "We developed very similar attacks, but we were a team of 10 researchers," he added.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.