Simply updating this barcode scanner app may have infected 10 million users with malware
While Google has removed the app from the Play Store, it remains installed on devices that already have the app installed. Malwarebytes alleges that the developer of the app intentionally added the malicious code in the update.
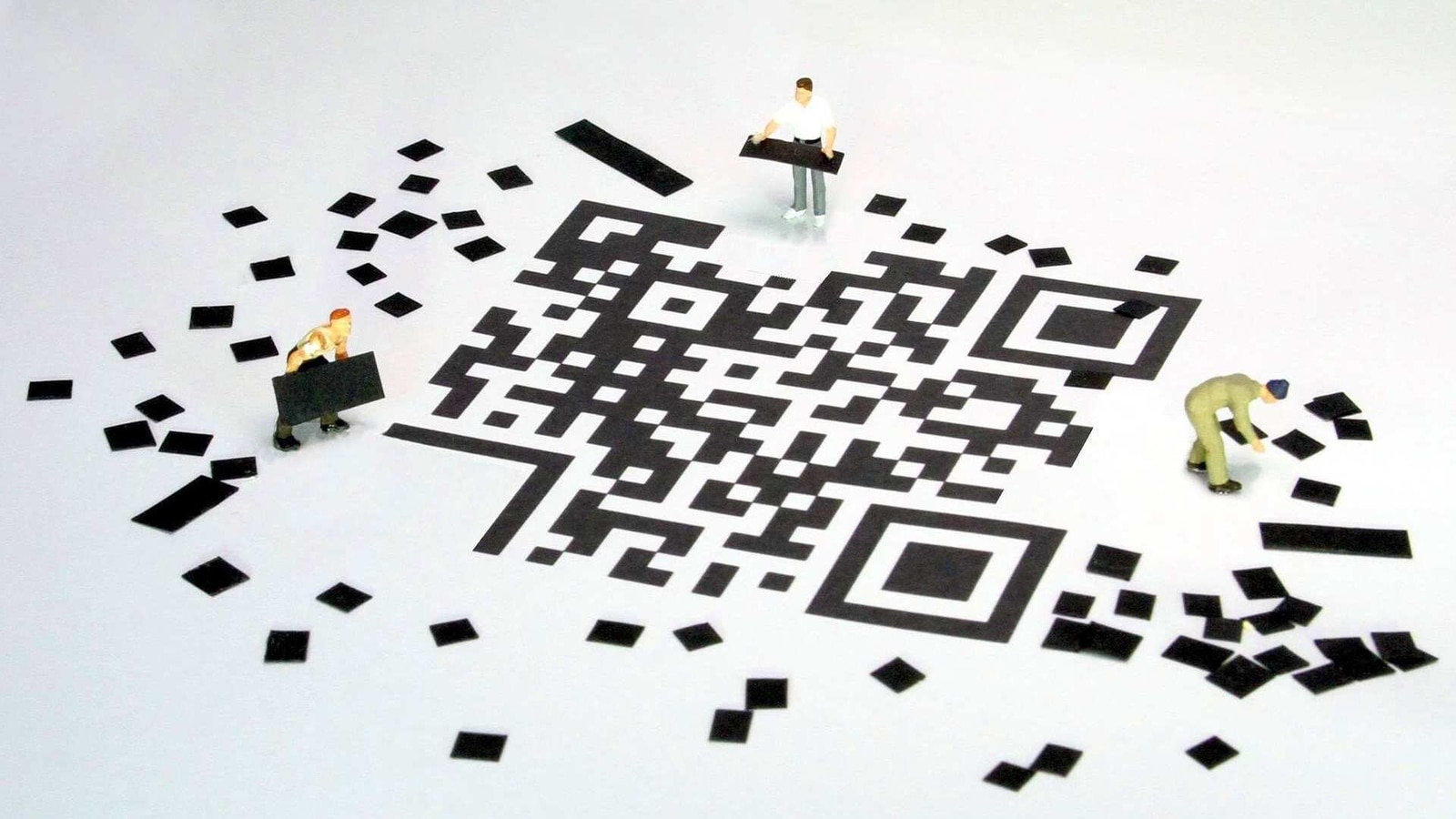
In what can clearly be labelled a sneaky move pulled on unsuspecting app users, a simple app update to a barcode scanner app on the Google Play Store has potentially infected over 10 million users, according to a reputable security software company.
In a blog post, Malwarebytes stated that in December last year, their users had reported a sudden appearance of ads in their default browser - all of a sudden, and with no interaction whatsoever. Security experts usually tell users to list out the most recently installed apps to identify any bad actors, but these users had not downloaded any new apps, especially not from outside the Play Store.
Also read: Facebook-based malware from 2016 is back, here are some tips to avoid it
The company said that one of its users, Anon00 identified that the infection was originating from an app that was installed a long while ago - Barcode Scanner by Lavabird LTD. The app was last updated on December 4. According to Malwarebytes, the app didn't lie dormant waiting for users to keep their phone aside, it activated itself within minutes of installing the update.
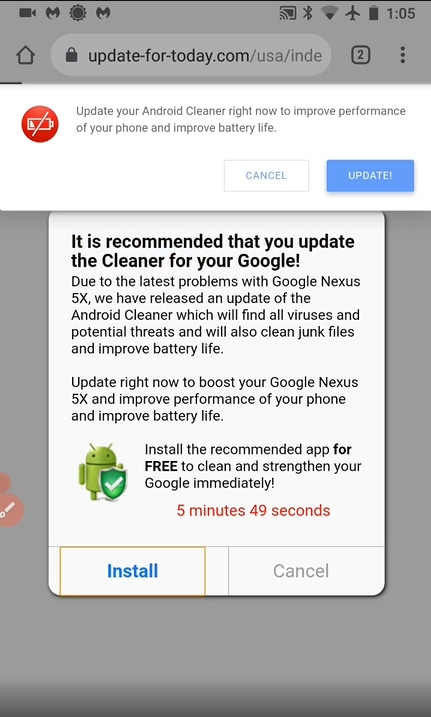
Users who had updated their app saw their default browsers open on their own, without any interaction and load a webpage that asked users to install a “cleaner” app on the Play Store, which ironically, also contains ads. The user would also see popups as well as messages styled like notification requests on the page, as illustrated in the image below.
How did this happen? For starters, most apps on the Play Store are monetised with the help of advertisements, which means they need to have various ad SDKs inside. While these ad SDKs allow the existence of free apps, it also means that when the SDK updates the app could also show more aggressive ads. Malwarebytes alleges that the developer of the app has intentionally added the functionality and has identified the app as a trojan due to “malign” intent.
Read more: Suspected Russian hackers targeted cyber firm Malwarebytes
Malwarebytes says that they added the ‘Android/Trojan.HiddenAds.AdQR' detection for the app, which means users with their malware scanner will be alerted that the app is unsafe and must be removed. Google has also removed the app from the Play Store, but it will remain installed on devices that already have the app. Users are advised to remove the app, if they do have it installed as their devices will most certainly be affected by this malicious app.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.































