Brave Browser fixes privacy flaw that could leak your Tor addresses
The browser developer had to disable one of its adblocking techniques to fix the privacy flaw and released a fix for the issue earlier this week.
There are many privacy-friendly alternative browsers for those looking to switch from those offered by software giants Google, Apple and Microsoft - including the upstart Brave browser. While Brave offers a wide feature set, one glaring privacy issue that was present for over a month has finally been patched, according to a report.
Read more: Brave brings decentralised web browsing with IPFS support
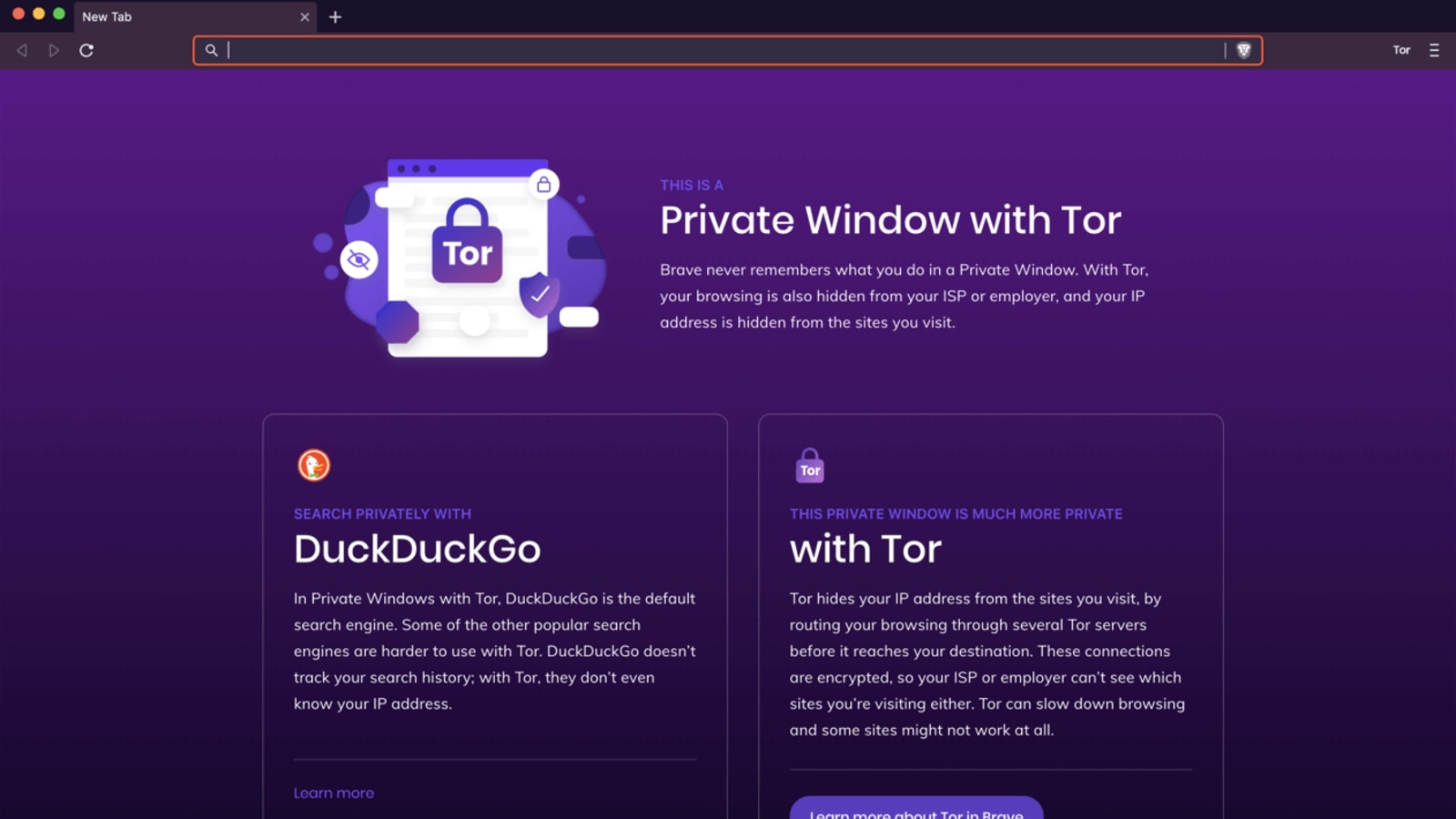
The privacy-oriented browser offers users the option to use The Onion Router (more commonly known as Tor) while browsing the web in Private Browsing Mode in order to further protect their privacy. However, the bug that was recently fixed reportedly leaked your Tor website URLs to your Domain Name Server (DNS) provider, according to a previous report by Bleeping Computer.
What does this mean? Websites on the dark web are only accessible using the Tor network and are supposed to be more privacy-friendly. However, since the bug would basically leak out the Tor address to your DNS provider (which is your Internet Service Provider for most people) it would defeat the entire purpose of using Tor.
Don't miss: Mozilla's Firefox 86 adds support for Multiple Picture-in-Picture mode and Enhanced Cookie Protection
The bug was first reported on Reddit, while another expert and Bleeping Computer also confirmed the claims - when verifying the traffic from a browser with Brave installed and connected to the Tor network. According to the latter, the security issue was caused by Brave's decision to connect to the Tor network via a proxy - meaning it did not offer the same privacy as the real Tor Browser.
However, the browser maker has already worked on a fix, which involves disabling the CNAME ad-blocking feature for Brave browser. According to the browser's latest release notes for version 1.20.110 released on Feb 24, (Fixed issue when visiting “.onion” URL in a normal window would cause DNS leak) it appears the issue has finally been resolved.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.































