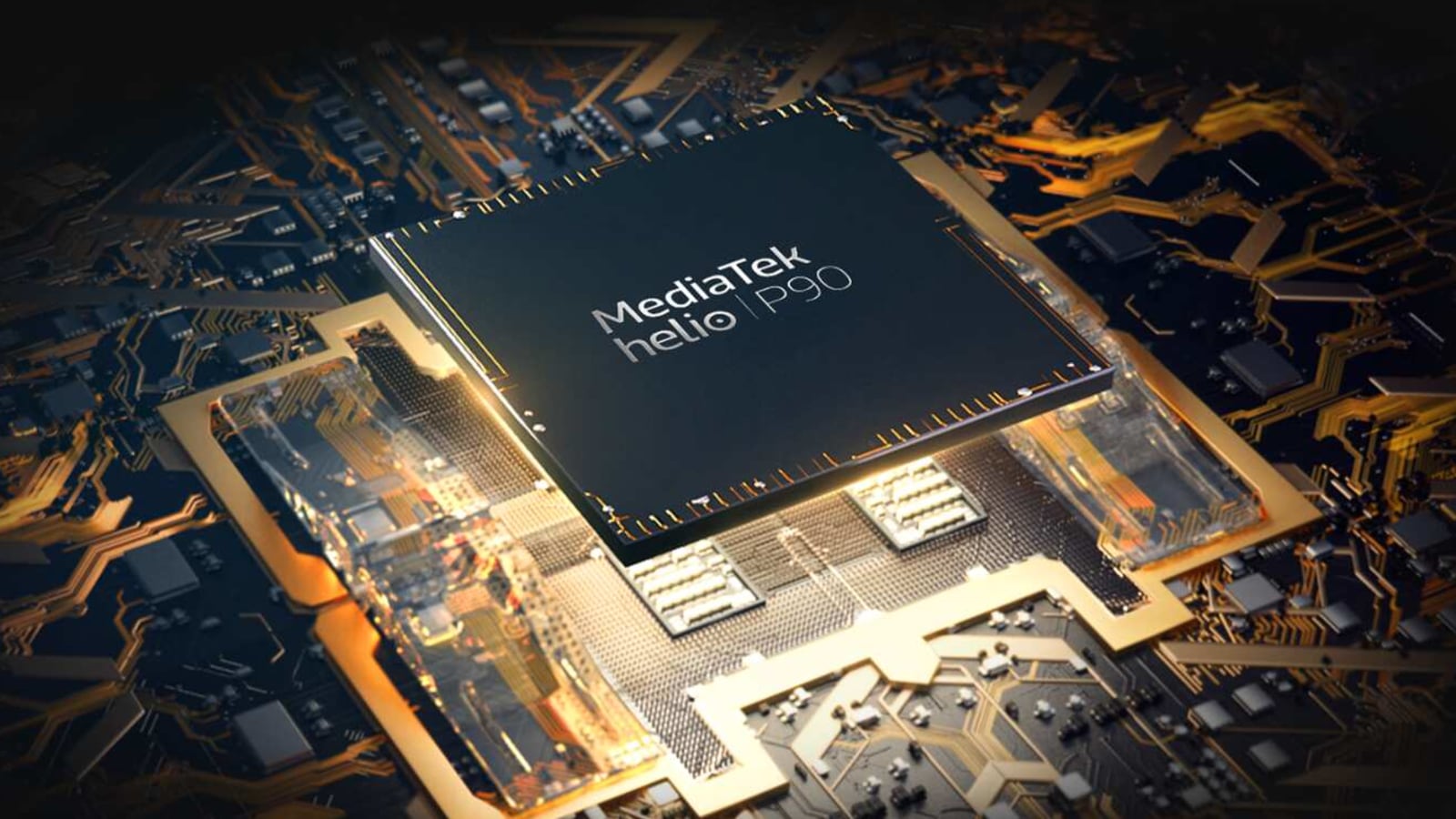
Bug in MediaTek chips could lead to hackers eavesdropping on Android users
Upon research, CPR researchers found out that MediaTek chips, that power 37% of the world’s smartphones including the ones from companies like Xiaomi, Oppo, Realme, and Vivo among others, have security flaws inside the chip's audio processor.
Time and again, we heard reports about zero-day vulnerabilities that could give hackers the necessary means to gain access to people's PC, smartphones or even smart home devices. Reports have also detailed how hackers use malicious apps to gain access to people's smartphones. Now, reports have detailed a bug that could lead hackers to eavesdrop on Android users.
Researchers from Check Point Research have identified security flaws in the smartphone chip made by Taiwanese manufacturer MediaTek. Upon research, CPR researchers found out that MediaTek chips, that power 37% of the world's smartphones including the ones from companies like Xiaomi, Oppo, Realme, and Vivo among others, have security flaws inside the chip's audio processor. If left unpatched, the vulnerabilities could have enabled a hacker to eavesdrop on an Android user and hide malicious code on the MediaTek-powered devices.
The report also detailed the process that hackers would have to go through to exploit this vulnerability. First of all, a user will have to install and launch a malicious app from the Google Play Store to give hackers a way to exploit the vulnerability in MediaTek SoC-powered smartphones. Once installed and launched, the app will use the MediaTek API to attack a library that has permission to talk with the audio driver. After that, the malicious app with system privilege will send crafted messages to the audio driver to execute code in the firmware of the audio processor. Once that happens, the app will steal the audio flow enabling hackers to eavesdrop on a users' conversations.
CPR in a blog post noted that this hack could be executed via three separate vulnerabilities, which include CVE-2021-0661, CVE-2021-0662, and CVE-2021-0663. Soon after, CPR researchers disclosed their findings to MediaTek, which fixed these vulnerabilities in October.
To put it simply, MediaTek has already fixed these vulnerabilities on all the smartphones running on its SoCs. All you need to do is ensure that you have downloaded the latest firmware and software update on your smartphone.
“Device security is a critical component and priority of all MediaTek platforms. Regarding the Audio DSP vulnerability disclosed by Check Point, we worked diligently to validate the issue and make appropriate mitigations available to all OEMs. We have no evidence it is currently being exploited. We encourage end-users to update their devices as patches become available and to only install applications from trusted locations such as the Google Play Store,” Tiger Hsu, Product Security Officer at MediaTek said in a statement.
Catch all the Latest Tech News, Mobile News, Laptop News, Gaming news, Wearables News , How To News, also keep up with us on Whatsapp channel,Twitter, Facebook, Google News, and Instagram. For our latest videos, subscribe to our YouTube channel.